Ranjith2000
August 29, 2023, 5:40pm
1
Hi All,
i need to restrict the request when the user raising the entitlement and it will check that entitlement belongs to abc application so if user have a account in abc application then that request will allow . if the user dont have the application link then block him saying "please raise request for “Role A” and get the account created.
i have tried in advance policy but it didnt work so now im trying to achieve this requirement in LCM Provisioning
my doubt is which sub workflows we can achieve this . iam thinking i need to write a logic in Identity Request Violation Review
can anyone help this
Thanks,
2 Likes
Hi @Ranjith2000 ,
The Policy works in conjunction with LCM Provisioning workflow when raising request.
policyScheme
policiesToCheck
allowRequestsWithViolations
2 Likes
Remold
August 29, 2023, 9:28pm
3
Using a policy is the way to go IMHO. It is much simpler, cleaner and no need to change OOTB workflows
With the Remediation Action you can state what needs to be done (please raise request for “Role A”).
Can you state what you tried with the advanced policy and what issues you faced?
– Remold
3 Likes
Ranjith2000
August 30, 2023, 2:02pm
5
Hi @Jarin_James @Jarin_James
import sailpoint.object.*;
import java.util.*;
import java.text.*;
import org.apache.log4j.Logger;
import org.apache.log4j.Level;
PolicyViolation violation = null;
boolean raisePaRequest=false;
if ( plan != null ) {
//List accounts = plan.getAccountRequests();
log.error("emtering list "+ accounts);
if ( ( accounts != null ) && ( accounts.size() > 0 ) ) {
for ( AccountRequest accountRequest : plan.getAccountRequests()){
String appNAme=accountRequest.getApplicationName();
String operation=accountRequest.getOperation();
if(appNAme.equalsIgnoreCase("AD Account") && operation.equalsIgnoreCase("Create") )
{
raisePaRequest = true;
}
}
}
}
if (raisePaRequest) {
String blockingMsg = "You cannot request Application Name Entitlement without Application Name";
violation = new PolicyViolation();
violation.setActive(true);
violation.setIdentity(identity);
violation.setPolicy(policy);
constraint.setName(blockingMsg);
violation.setConstraint(constraint);
violation.setDescription(blockingMsg);
violation.setStatus(sailpoint.object.PolicyViolation.Status.Open);
}
return violation;
this is rule which i was trying in lcm provsioning but which subprocess i need to put into this rule
can anyone please help this
Thanks
1 Like
HI @Ranjith2000
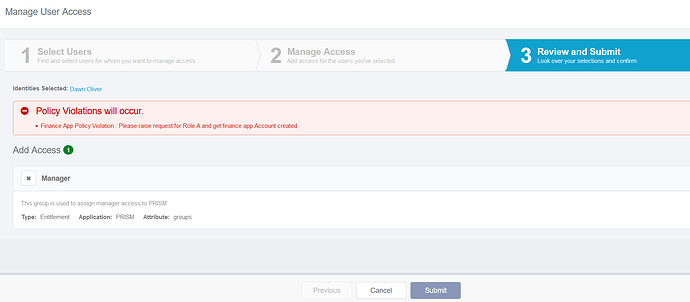
Just to clarify your requirement,AcctsPayable entitlement in finance app “Please raise request for Role A and get Active Directory Account created”
1 Like
Ranjith2000
September 1, 2023, 6:09am
7
Hi @Jarin_James
yes exactly that is my requirement ,AcctsPayable entitlement in finance app
sorry that violation meseages " “Please raise request for Role A and get finance app
1 Like
Hi @Ranjith2000
You try below code snippet for Advanced Policy
import java.util.List;
import java.util.Locale;
import sailpoint.api.IdentityService;
import sailpoint.api.SailPointContext;
import sailpoint.object.Application;
import sailpoint.object.Entitlement;
import sailpoint.object.GenericConstraint;
import sailpoint.object.Identity;
import sailpoint.object.Link;
import sailpoint.object.Policy;
import sailpoint.object.PolicyViolation;
import sailpoint.tools.GeneralException;
private String policyMessage = "Please raise request for Role A and get finance app Account created";
String applicationName = "finance app";
String entitlementValue = "AcctsPayable";
public PolicyViolation generatePolicyViolation(Identity identity, Policy policy, GenericConstraint constraint, String policyDescrptn) {
PolicyViolation policyViolation = new PolicyViolation();
policyViolation.setActive(true);
policyViolation.setIdentity(identity);
policyViolation.setPolicy(policy);
policyViolation.setConstraint(constraint);
policyViolation.setDescription(policyDescrptn);
policyViolation.setStatus(sailpoint.object.PolicyViolation.Status.Open);
return policyViolation;
}
public List fetchIdentityEnt(Identity identity, String applicationName) {
List applicationLinks = identity.getLinks();
List entitlementList = null;
if(applicationLinks != null && applicationLinks.size() > 0) {
for (Link singleIdentityLink : applicationLinks) {
if (applicationName.equals(singleIdentityLink.getApplicationName())) {
try {
entitlementList = singleIdentityLink.getEntitlements(Locale.getDefault(), "");
} catch (GeneralException e) {
log.error("The Error is: " + e);
}
}
}
}
return entitlementList;
}
public boolean isPolicyViolated(Identity identity) throws GeneralException {
log.debug("Entering isPolicyViolated");
boolean isPolicyViolated = false;
boolean entitlementExist = false;
boolean linkExist = false;
String name = identity.getName();
log.debug("name = "+ name);
Identity oldIdentity = context.getObjectByName(Identity.class,name);
log.debug("oldIdentity = "+ oldIdentity);
Application application = context.getObjectByName(Application.class, applicationName);
IdentityService identityService = new IdentityService(context);
if(oldIdentity != null){
List links = identityService.getLinks(oldIdentity, application);
log.debug("links = "+ links.size());
if(!links.isEmpty()){
linkExist = true;
}
}
List entitlementList = fetchIdentityEnt(identity, applicationName);
log.debug("entitlementList = "+ entitlementList);
if(entitlementList != null){
for(Entitlement entitlement : entitlementList){
if(entitlement.getAttributeValue().equals(entitlementValue)){
entitlementExist = true;
break;
}
}
}
log.debug("linkExist = "+ linkExist);
log.debug("entitlementExist = "+ entitlementExist);
if(!linkExist && entitlementExist){
isPolicyViolated = true;
}
log.debug("isPolicyViolated = "+ isPolicyViolated);
log.debug("Exiting isPolicyViolated");
return isPolicyViolated;
}
log.debug("*****************Inside Finance App Policy Violation Rule***********************");
boolean isPolicyViolated = false;
PolicyViolation appPolicyViolation = null;
List entitlementList = fetchIdentityEnt(identity,applicationName);
try {
if (identity != null) {
isPolicyViolated = isPolicyViolated(identity);
}
if (isPolicyViolated) {
appPolicyViolation = generatePolicyViolation(identity, policy, constraint, policyMessage);
}
} catch (GeneralException e) {
log.error("General Exception " + e);
}
log.debug("appPolicyViolation = "+ appPolicyViolation);
return appPolicyViolation;
This should throw the user with Violation. I have tested with a different application, and it is working.
Update the Rule summary with the desired message;
3 Likes
Ranjith2000
September 1, 2023, 11:04am
9
Thanks you So Much @Jarin_James this rule was perfectly working for my requirement
3 Likes
Hi @Jarin_James ,
Greetings! I would like to ask a query on your valuable response on advanced policy, hope you don’t mind.
What could be the reason I am not getting the block message displayed in “Manage User Access” while submitting the request. Seems like I am getting an detective policy instead. When simulation ran the count of violations where not zero. We are using IIQ.8.3.
Hi @The_IAMSheriff ,
Can you check the policyScheme Variable in LCM Provisioning Workflow. It shouldn’t be disabled and should be interactive to allow the requestor to remove the request.
1 Like
Seems like it, thank you Jarin.
system
December 29, 2023, 11:18am
13
This topic was automatically closed 60 days after the last reply. New replies are no longer allowed.